Software
On this page, I'll discuss the use of a few handy applications, as well as presenting some of the programmes I wrote in my younger days :)
You can check out my first few Java applets on my page The RSA Code.
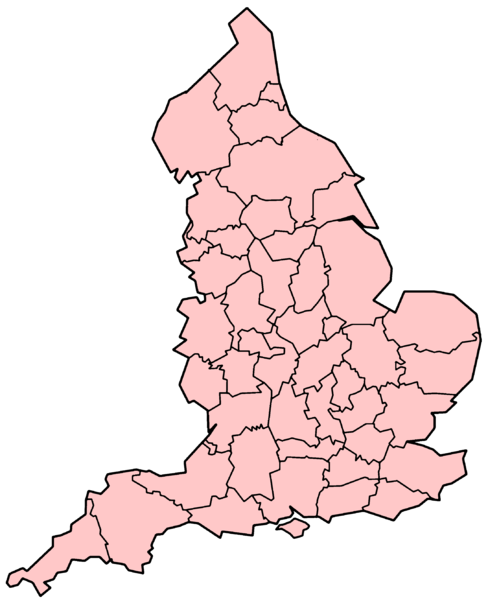 The 48 Counties of England
The 48 Counties of England
Or, more precisely, the 48 Ceremonial Counties of England. As with most things English, the notion of a county is simultaneously ancient and ever-changing. Currently, there are two useful notions of Counties, the Ceremonial Counties and the "Metropolitan and non-metropolitan counties and unitary districts", the latter numbering 82.
The MANM Counties and unitary districts are administrative divisions in local government and include such oddities as Warrington, Medway, and Halton, to name but three. Conversely, the 39 Historic Counties include sadly defunct entities such as Middlesex and Huntingdonshire.
The Ceremonial Counties occupy a sane middle ground between the two extremes. They are characterised by each having a Lord Lieutenant appointed to them. For instance, the current Lord Lieutenant in my county of Oxfordshire is Hugo Brunner JP. The Lord Lieutenant is the representative of the Crown in their lieutenancy. As such, their most important duty is to escort members of the Royal family on visits to their county.
All this is apropos of a little online quiz I've made to test your knowledge of the ceremonial counties. Do click the link if you're interested!
Update! I've now written a version for our friends across the pond. So please try out my 50 States of the USA quiz.
GnuPG and Friends
Installation of GnuPG
GnuPG is the GNU Privacy Guard — an open source replacement for PGP. GnuPG can be used for encrypting and/or signing emails and other documents.
I'm going to describe the process of setting up GnuPG with Microsoft Windows XP. Another short guide is to be found on mozdeg.org. The canonical reference is the Gnu Privacy Handbook.
First you need to download a copy of GnuPG, verify its authenticy, then install it. The instructions for so doing are to be found on the GnuPG website.
Having installed the software, I recommend adding GnuPG to your
%PATH% environment variable. To do this, right-click on "My
Computer", select Properties, then Advanced, then Environment
Variables. Add (if it doesn't exist) or Edit (if it does), the User
Variable "PATH". Add the value C:\Program
Files\GNU\GnuPG. You may
now access gpg from the command line.
Your personal data will be stored in %APPDATA%\gnupg.
Typically,
if your username is Bob, the personal data will be stored in
C:\Documents and Settings\Bob\Application Data\gnupg.
If you already have some keys from another installation of GnuPG
(which will be found in files called secring.gpg and
pubring.gpg), you may import them with gpg --import
filename.
If you don't already have your own keys, you'll have to generate
them with the command gpg --gen-key. Follow the
instructions. I recommend generating a key-pair which doesn't expire,
though this can be changed later.
Make your passphrase fairly long!
Keyservers
Your key is useless unless you can share it with others.
One way to share your key is to use a keyserver. First find the keyID
of your public key with gpg --list-keys. The keyID is an
8-digit hexadecimal number. The keyID for one of my public keys is
CC144DA2. We'll use this in the following examples.
Before sending the key to a server, it's a good idea to create a
revocation certificate. You'll need this if your key is every
compromised. The revocation certificate is used to inform a server
that the key has been revoked. The syntax for the creation of a
revocation certificate is gpg -a --output filename
--gen-revoke CC144DA2.
We may now add our public key to a key server. Here is the command:
gpg --send-keys --keyserver pgp.mit.edu CC144DA2
Enigmail
Now we need to do something useful with GnuPG! I assume you're
using the Thunderbird/Mozilla email client. Find and install the
enigmail extension. The only setup required is to tell enigmail where
to find GnuPG. Close down and restart Thunderbird (if you haven't
done so already). Loacte the OpenPGP menu and select Preferences.
For the GnuPG executable path, enter C:\Program
Files\GNU\GnuPG\gpg.exe. It should be fairly clear how to
operate Enigmail.
Fingerprints; the Web of Trust
I mentioned that a key pair is only useful if the public key is shared. However, you need to ascertain that a key you find (from a keyserver, for example) really does belong to the person it claims to. This is where fingerprints enter the picture.
Each key has a fingerprint associated with it. If you download a
key, you can contact the key's owner in person to find out the key's
fingerprint. If the fingerprints match, you can be almost certain
that you have found a valid key. You can find the fingerprint of a
key by
entering gpg --fingerprint keyID. Once you are
certain of the authenticity of a key, you may sign it with your
own secret key. Having signed the key, you may send the updated key
to a keyserver (note, you will be sending someone else's key to the
keyserver!).
Anyone who subsequently downloads the key from the server will see that you have placed your seal of approval on the key. If they have a validated copy of your key, this may give them some level of confidence that the key is authentic, without having to check the fingerprint themselves. In fact, GnuPG has a built-in system called the web of trust which automates this process to some extent.
For more information on these issues, please refer to the GNU Privacy Handbook.
 Noseguy
Noseguy
A 'game' I created using blender. There is no actual goal in the game, but you can move around by using the cursor keys, the A and Z keys and the space bar (should be easy to figure out what the keys do!). This game is in the form of a zipped Linux and Windows binaries for x86 machines.
Spcaview Patch
This is a patch for the spcaview webcam software for linux. The patch provides an automatic brightness adjustment facility. Installation instructions are included.
Update: the patch has now (as of 17/08/2004) been applied to the official driver.
Camserv Patch
This is a patch for the camserv webcam server for linux. The patch improves the speed performance of the autobrightness code. Installation instructions are included.
Konnect4
Download Win32 version, self-extracting archive (127K)
Download Win32 version, zipped (106K)
Download Linux version, tarred & gziped (16K)
This is my first internet program. It is an internet version of a children's game of a similar name. A help system is provided. (Please read the README file for instructions). Important note for Windows Users!! The Windows version of konnect4 needs a dynamic link library called cw3215.dll. This file is distributed with the zip file and the self-extracting archive. If konnect4 is to run properly, then cw3215.dll must be in the current directory (i.e. the directory which konnnect4 is run from), a directory in your PATH, your Windows directory or the System subdirectory of your Windows directory
 Fire
Fire
This programme could be viewed as a heat flow or diffusion model, but, more realistically, it just draws pretty pictures. The source code is in C, but I'm not giving out the source code for this one, as it evolved, rather than being planned, so the code is almost as untidy as my bedroom. (N.B. This is my personal favourite)
Numbers
In the UK, there's a popular television quiz program called
Countdown. One of the games on the show is the
numbers game. Seven numbers are chosen pretty
much at random, and the contestants have
to form the seventh number by means of
arithmetical operations on the first six
numbers. For instance, if the seven numbers
were 5, 3, 4, 8, 25, 50 and 657, then you'd
form the answer as 657 = 4+3+50*(5+8). My
programme takes as its input the seven
numbers, then tries to find an arithmetical
expression involving the first six which gives
the seventh (i.e. it solves the
problem).
Note
: This programme is for PC's running Linux.
Note also that my program is very slow :(
There are much better implementations to be
found on the web, e.g. look up Thaddaeus
Frogley on Google.
 Mandelbrot
Mandelbrot
This is a simple C++ programme which displays a fractal known as the Mandelbrot set. There are other programmes out there which do the same thing much faster (eg. FractInt), but I haven't got any of them. If you really want the source code for this, or any of the sequel, email me. (btw. the menu options for loading images and displaying instructions have not been implemented yet (and probably never will be.) sorry.)
Rerverse Polish Notation Pop-Up
This is rather an odd one, and only for hardened DOS
users. rptsr is a scientific
calculator pop-up, though it does require the
user to enter expressions in reverse polish
notation (no, I don't know why it's called
polish).
In reverse polish notation, the
arguments of an operation always
preceed the operator. For instance, where one
would normally write 3+4, in reverse polish
notation, we write 3 4 +
Get the
idea?
As a more sophisticated exmaple,
consider the following:
- (4 * (2 + 3)) ^ sin(9 + 10)
- Which becomes:
- 2 3 + 4 * 9 10 + sin ^
 Graphical Calculator
Graphical Calculator
This one is for Windows 3.x or later, and is a graphical version of the reverse polish notation calculator. Nuff said.